When identity and physical access are not enough
In security-critical environments, it is not enough to know who a person is.
To grant access, the individual must also have the right competence, have reviewed relevant safety regulations, and meet the requirements for the specific site, role, or task.
This is where Inphiz comes in.
A traditional identity system or an overarching IAM system (Identity Access Management) manages identity, roles, and physical access. Inphiz complements this by ensuring that the person is also validated, informed, and traceably approved before access is granted or maintained.
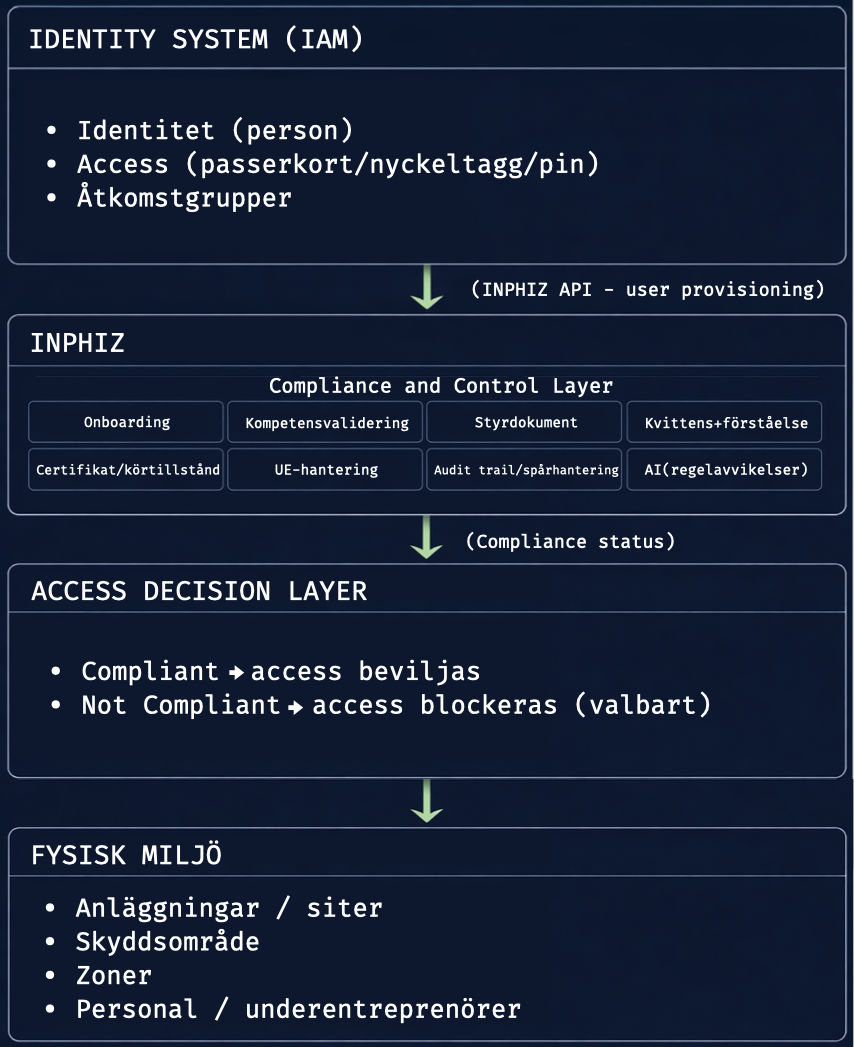
IAM manages identity.
Inphiz manages compliance.
An IAM system is designed to answer questions such as:
- Who is the person?
- What role does the person have?
- Which access group does the person belong to?
- Which card, account, or authorization object should be used?
- Can this be demonstrated afterward during an audit, incident, or inspection?
Inphiz answers what is often missing in the same flow:
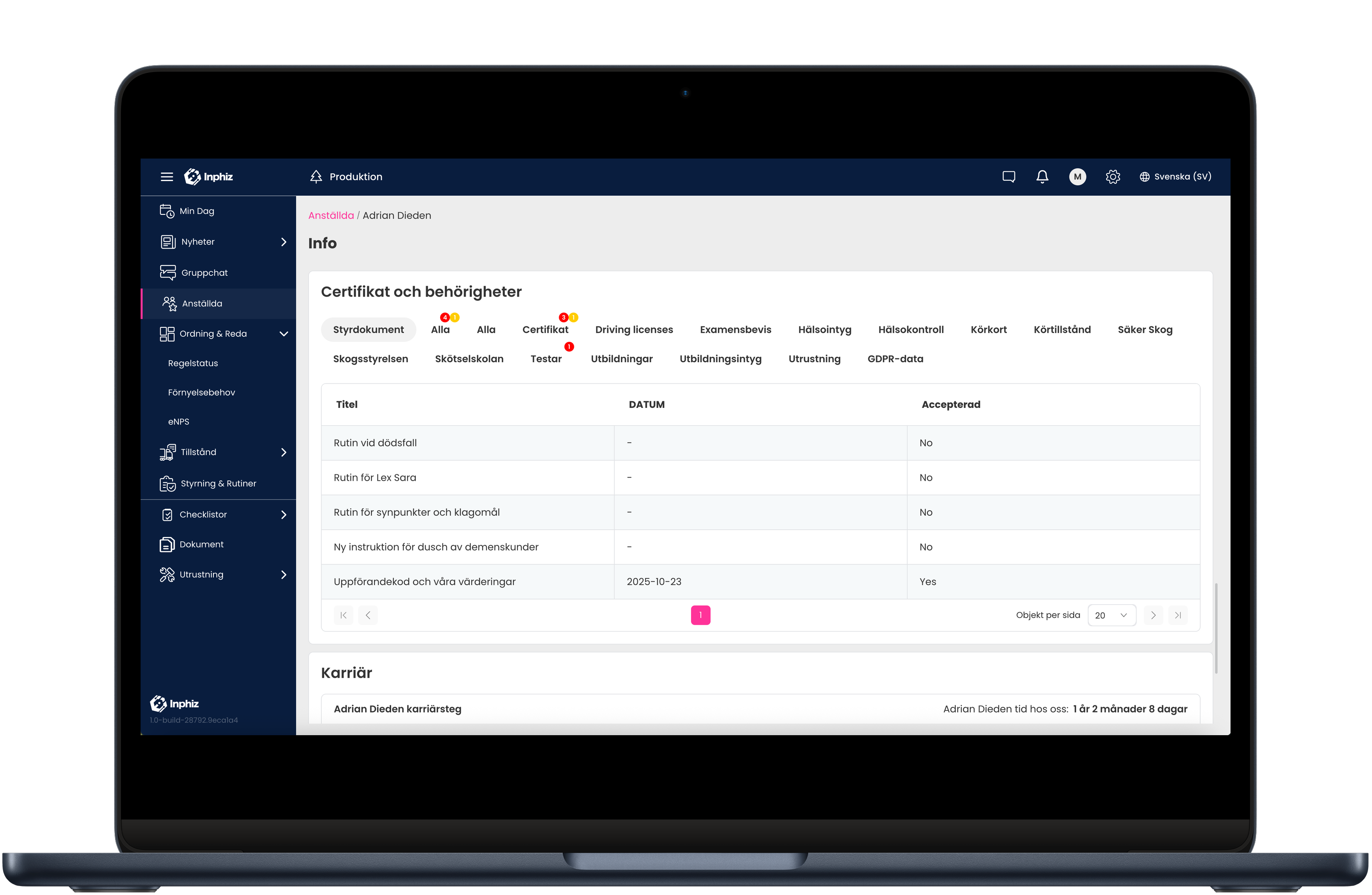
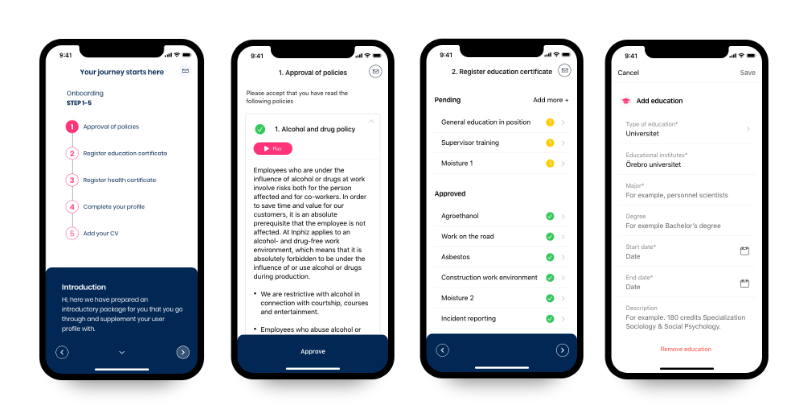
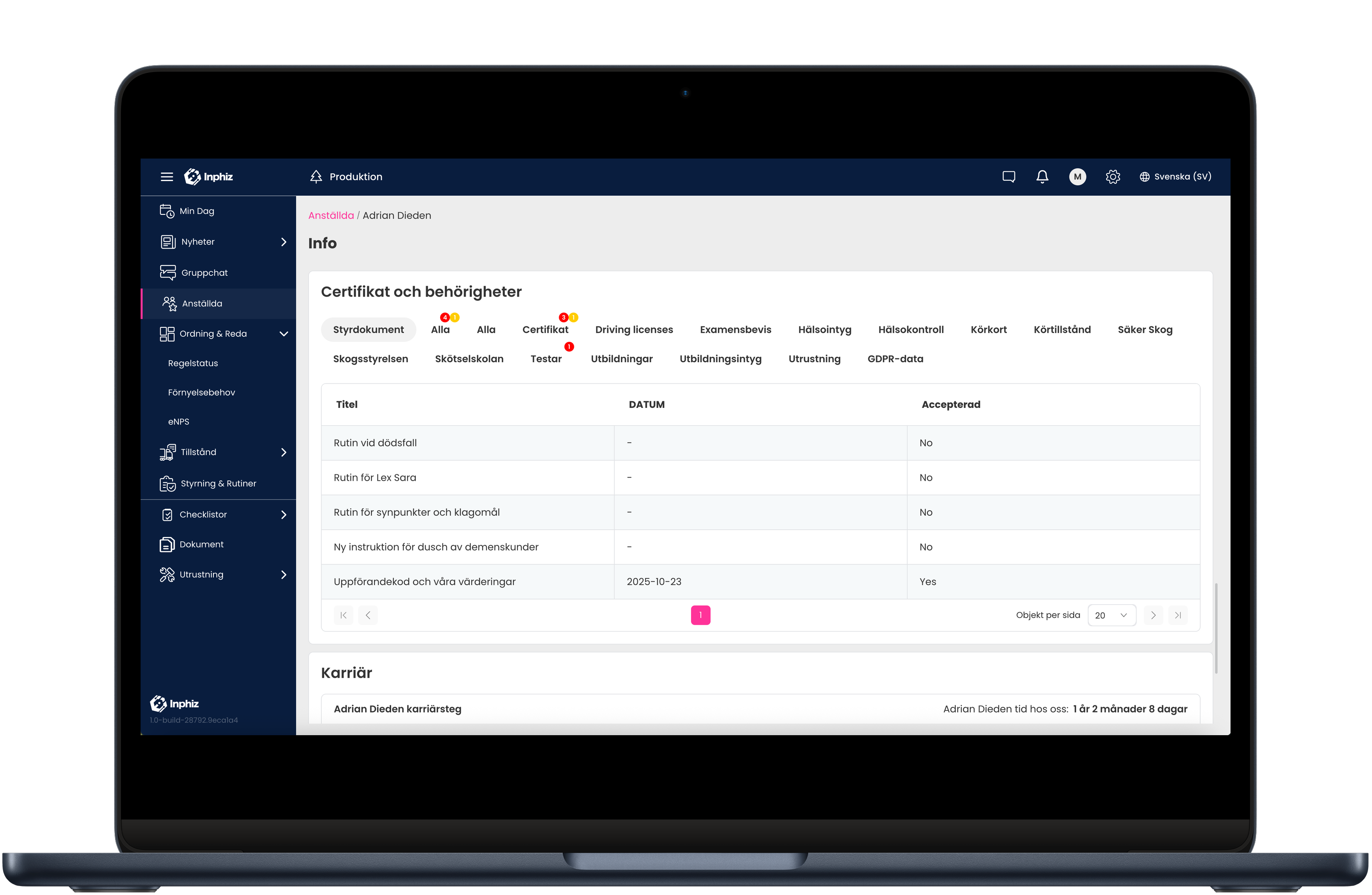
- Has the person completed the correct onboarding?
- Has the person read relevant rules and instructions?
- Has the person understood and confirmed governing documents?
- Does the person have the required training, certifications, or local permits?
Together, IAM systems and Inphiz create a complete model where physical security is combined with documented compliance.
From technical access to verified authorization
With Inphiz, access is no longer just a technical permission.
It becomes a verified, rule-based, and traceable authorization.
This means access can be linked to requirements such as:
- Onboarding for a specific site or operation
- Local safety regulations
- Training requirements
- Certifications and credentials
- Work-related permits
- Recurring confirmations of updated documents
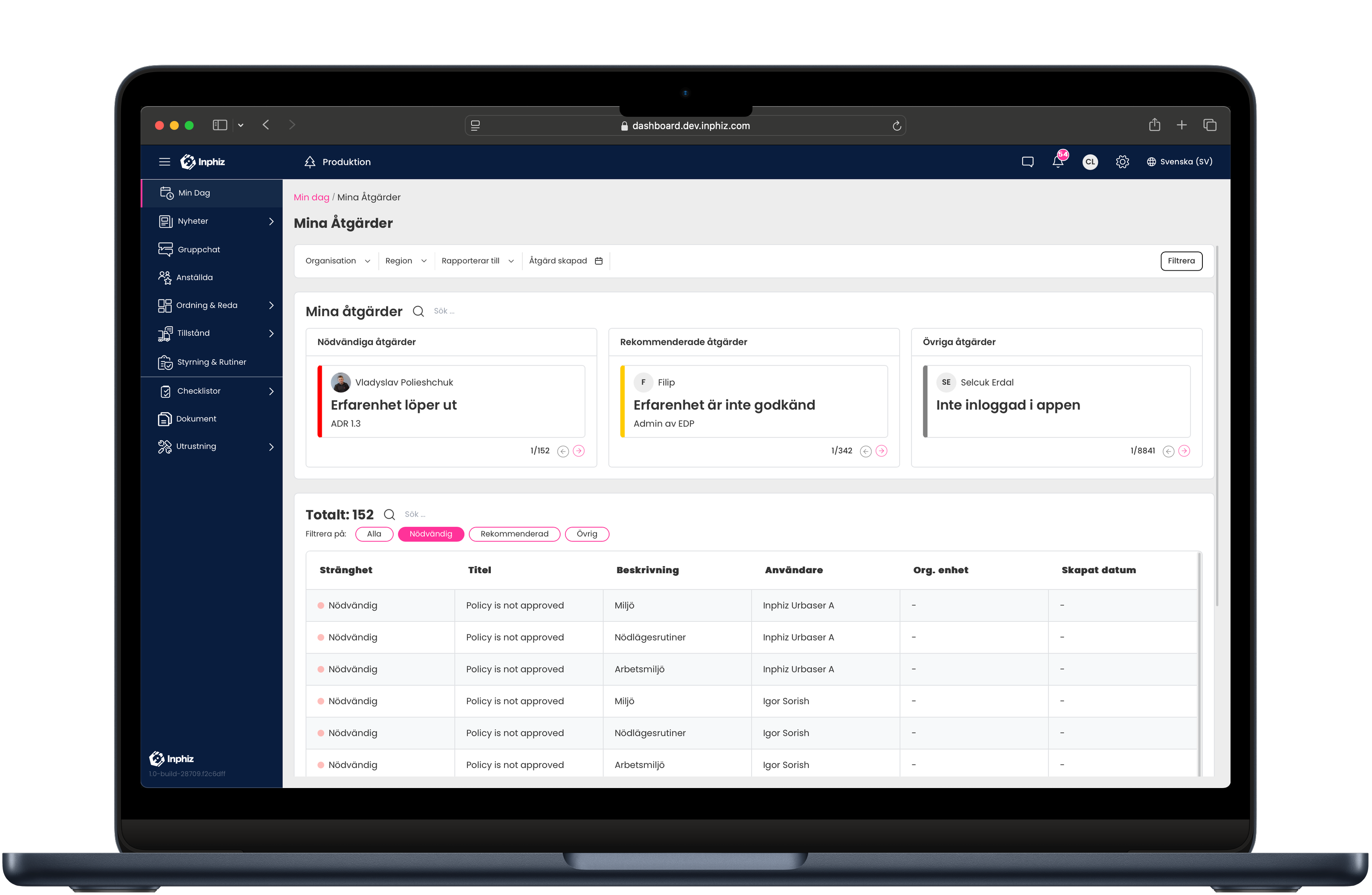
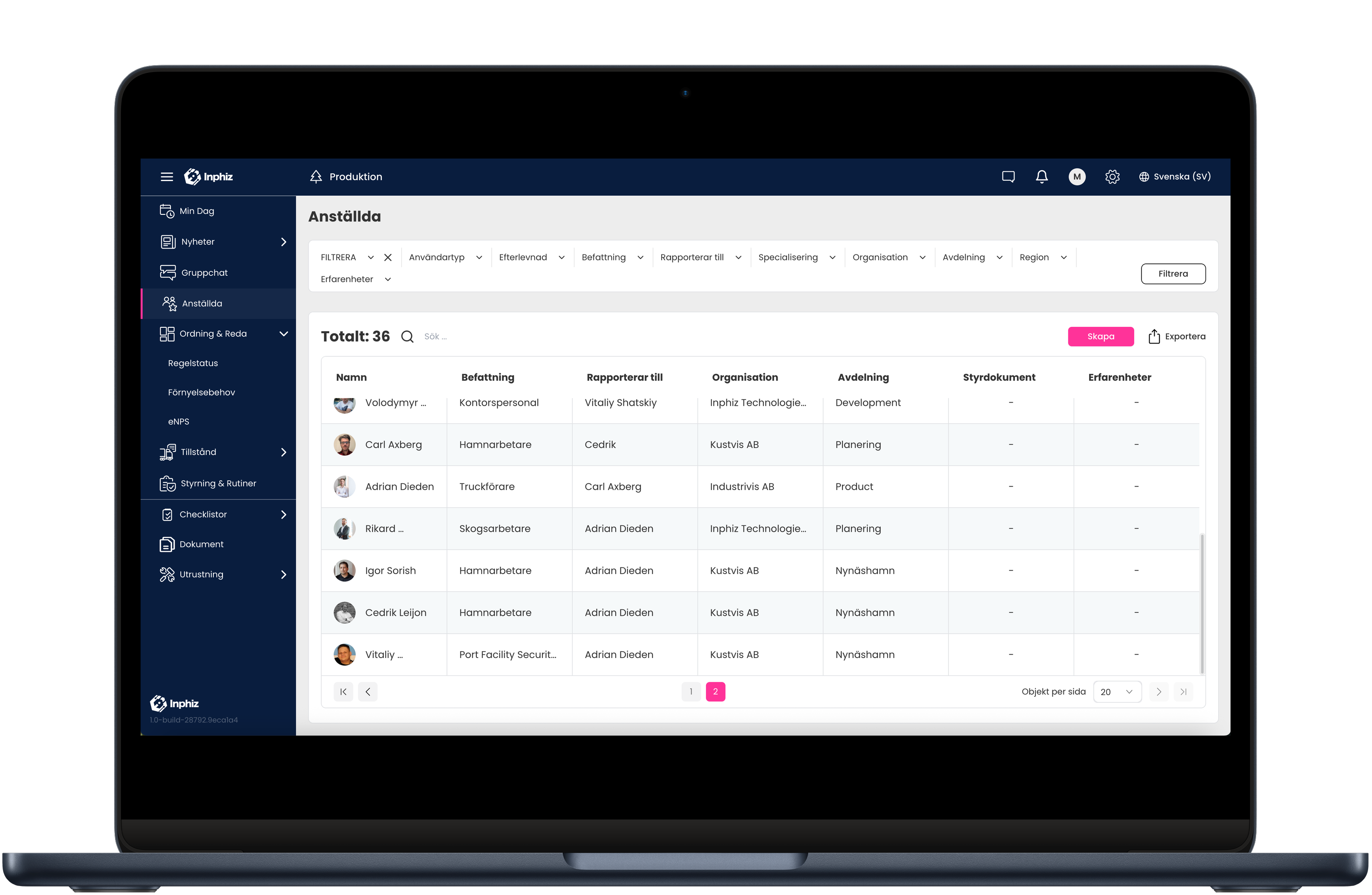
This provides better control over employees, contractors, subcontractors, and other external actors.
How the process works
- The individual is registered in the organization’s IAM system
- Identity and basic access information are managed there
- Inphiz activates the appropriate onboarding and validation requirements based on role, location, or access level
- The individual completes required steps, such as:
- reading governing documents
- confirming understanding
- registering competencies
- being validated against local requirements
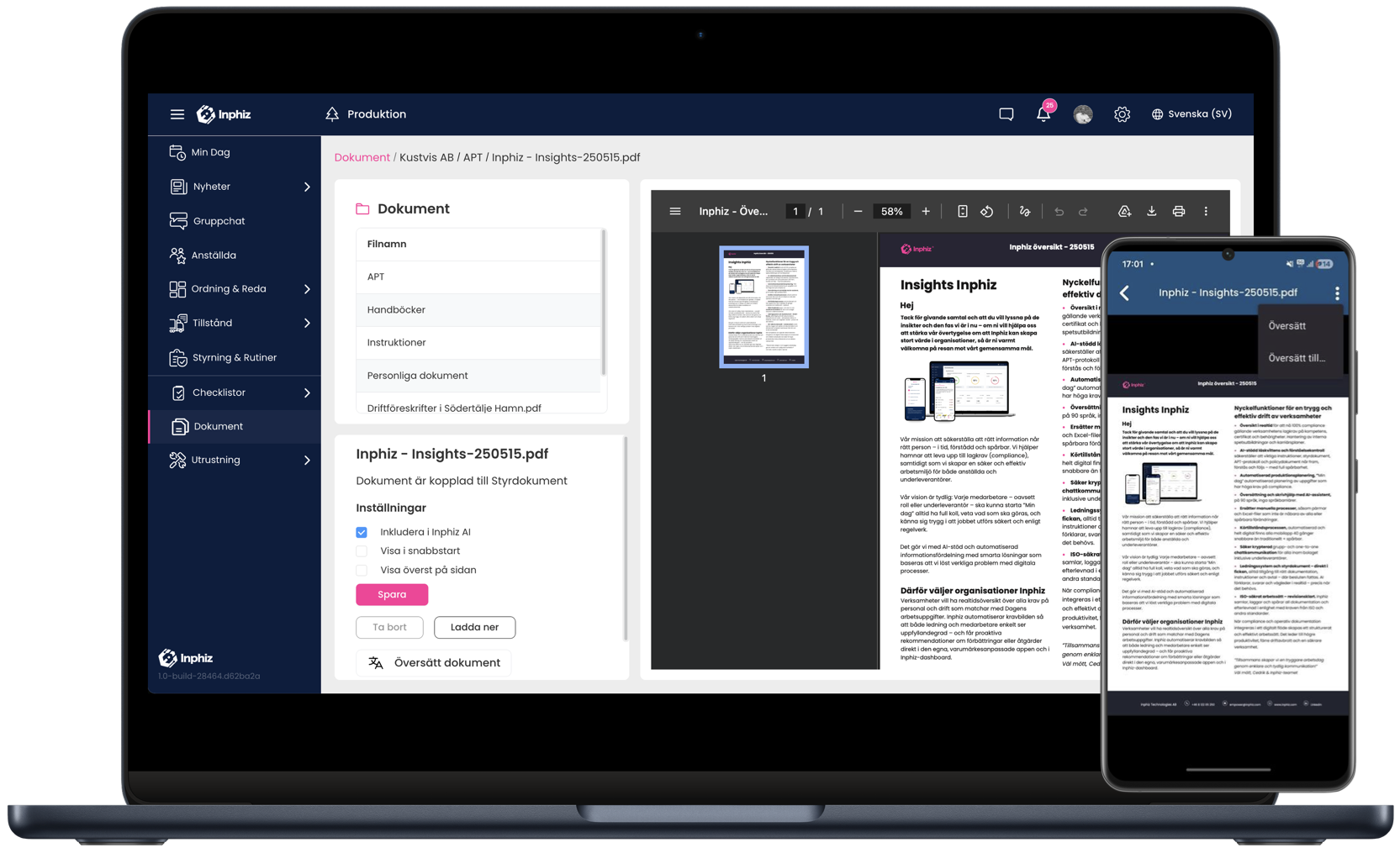
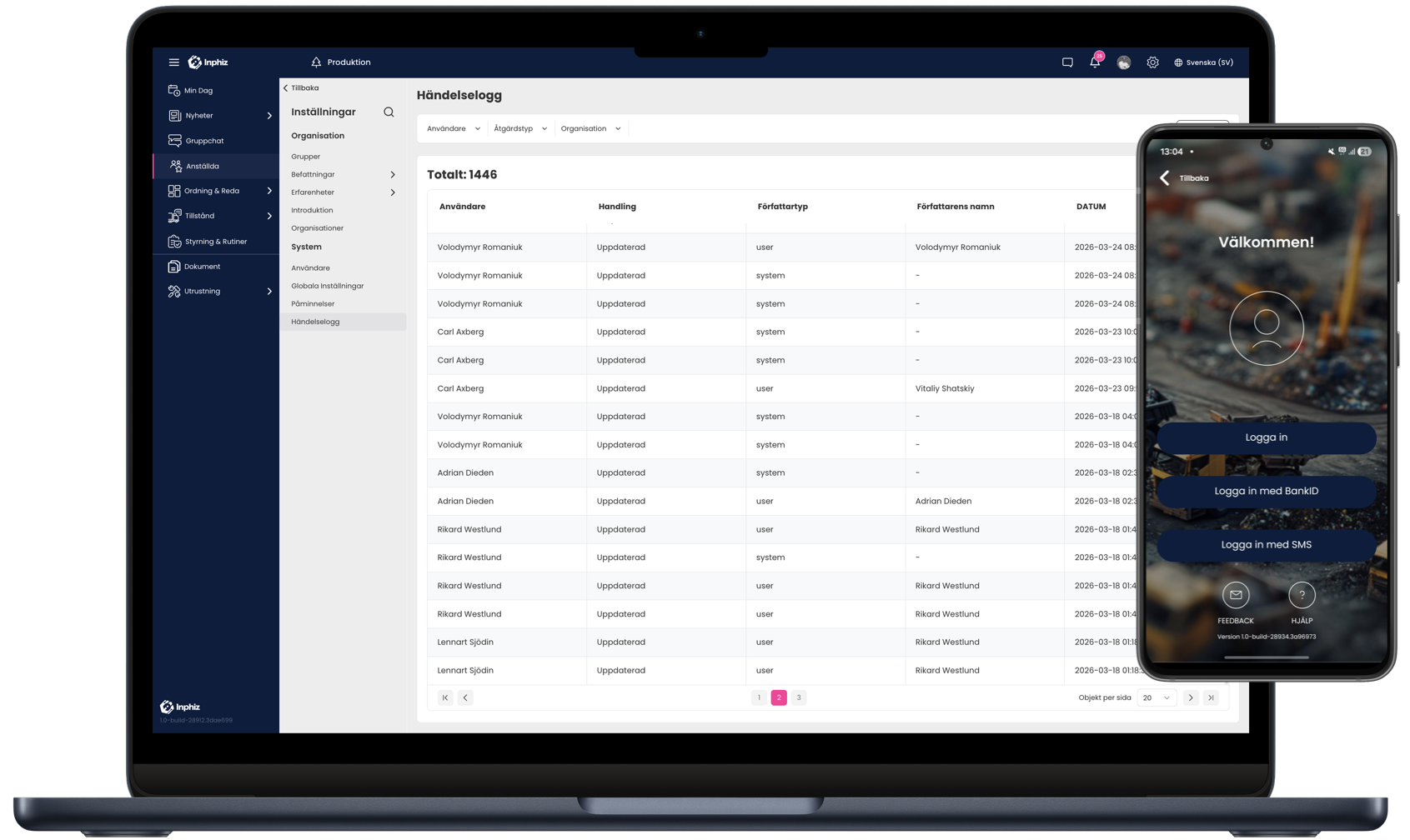
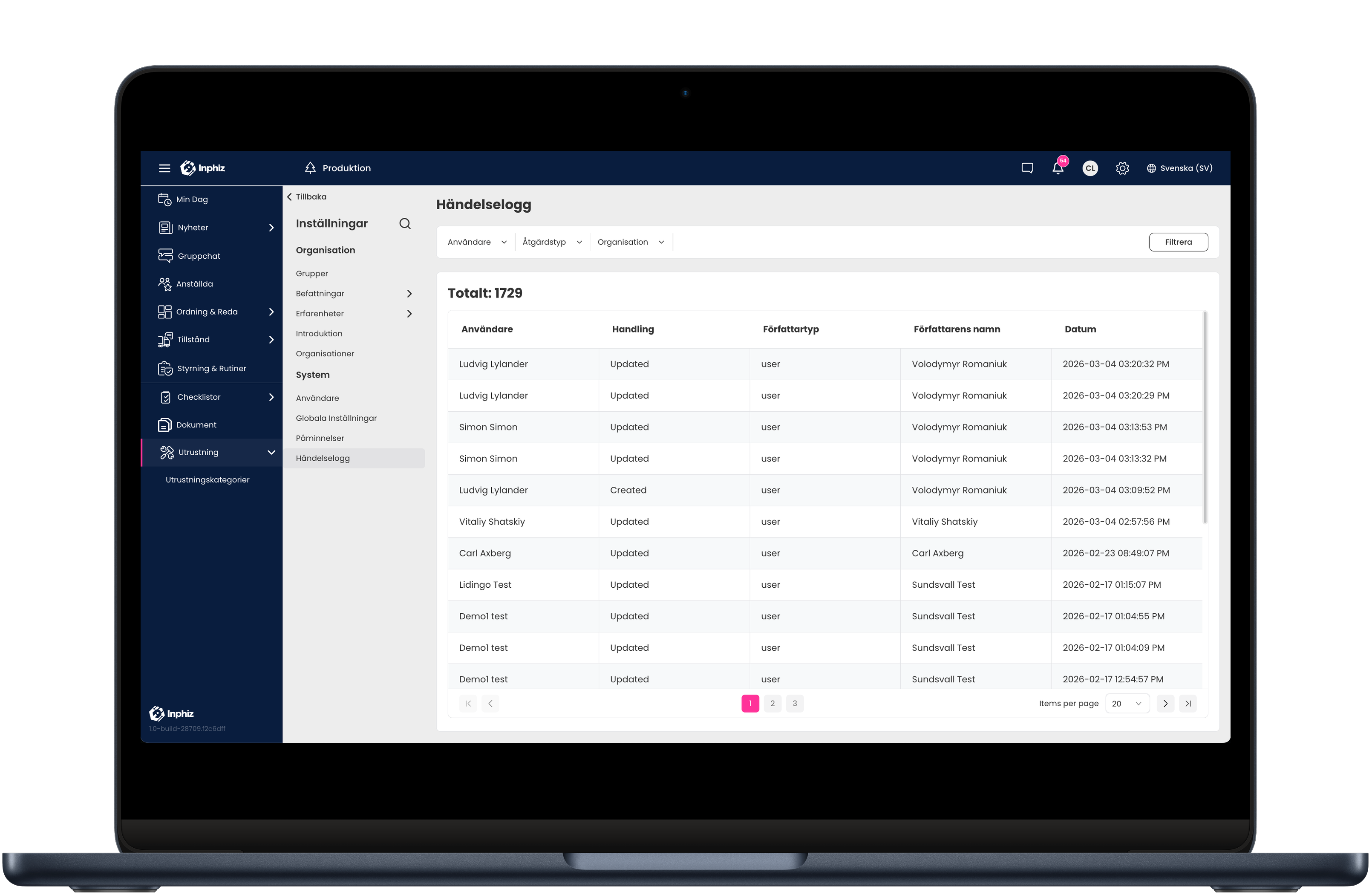
- Inphiz logs every step with timestamps, version history, and full traceability
- The organization gains a clear overview of which individuals are ready, approved, or missing required steps
The result is a structured, digital process where compliance can be monitored in real time.
People Compliance
Hanterar regelefterlevnad
på ett enkelt sätt
People Productivity
Ökar produktivitet med
automatiserade processer.
People Communication
Gör kommunikation enkelt
& tillgänglig för alla inom organisationen
People Onboarding
Ser till att nyanställda är
redo från dag ett och skapar
strukturerad master data
People Self service
Ger den anställda möjlighet
att själv styra sitt arbete i
rätt riktning
Inphiz gör ditt dagliga arbete enkelt
Inphiz förenklar ditt dagliga arbete och får dina medarbetare att prestera bättre, tillsammans. Inphiz är den moderna tjänsten för medarbetarengagemang och regelefterlevnad, skapat för små och stora företag som vill arbete smidigare och säkert. Med Inphiz ger du din organisation möjlighet att fokusera på det som verkligen gör skillnad för ditt företags framgång och dina anställda.
Produktivitet
Inphiz produktivitet är verktygen som gör att din dag går från hektisk till strukturerad och smidig. Med hjälp av automatiserade processer gör Inphiz det enkelt för dig och dina medarbetare att se vad som sker härnäst och ökar produktiviteten. Läs mer om hur Inphiz får din dag att gå på autopilot.
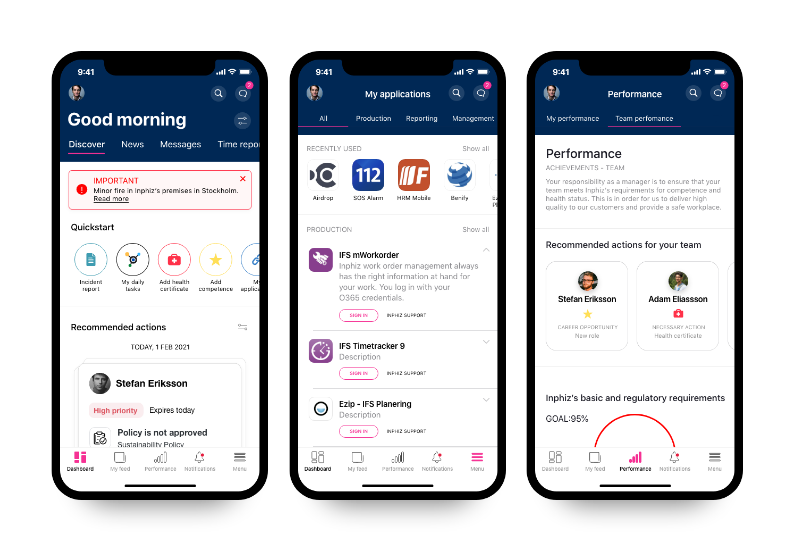
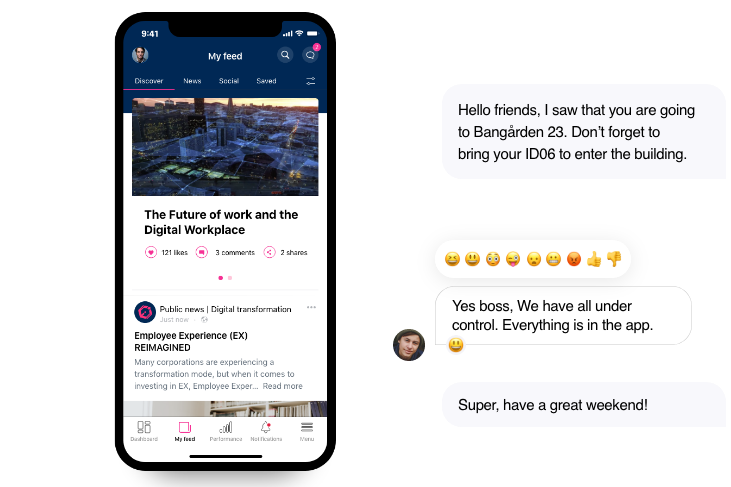
Kommunikation
Se till att dina medarbetare är informerade vart de än befinner sig. Inphiz gör intern kommunikation enkel och tillgänglig för alla. Skapa en kultur av samarbete och delning, och få dina medarbetare att känna sig hörda och en del av konversationen. Läs mer om hur de svåra med i företagskommunikation blir enkelt!
Onboarding
Ge dina anställda det välkomnande de förtjänar. Tillåt dina medarbetare bekanta sig med sina nya roller och säkerställ att de är redo innan de börjar sin första dag på arbetet. Inphiz onboarding inkluderar t ex praktiskt information, godkännande av policies, registering av kompetenser & intyg, uppsättning av personlig profil vilket ger den nyanställda ett gott första intryck.
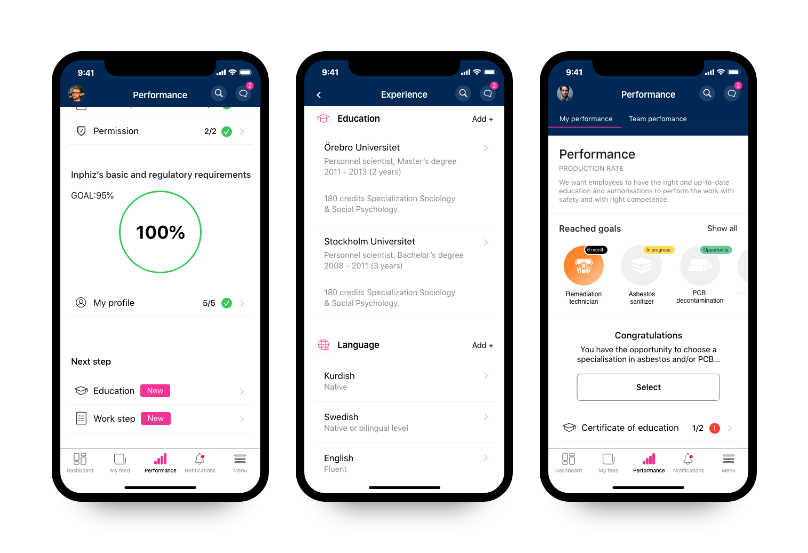
Självservice
Med Inphiz Self Service hanterar den anställda enkelt sin personliga profil och karriärvägar som styrs av satta regler för organisationen. Kan gälla personuppgifter, inställningar, erfarenheter, kompetens, certifikat, intyg, policyers och arbetsprocesser för att säkerställa att arbetet driver och följer förordningar och regulatoriska krav.
Support for regulatory requirements
IInphiz helps organizations work more systematically with requirements related to physical security, information security, and critical infrastructure.
-
ISPS Code (IMO / SOLAS XI-2)
-
National transport and port-related regulations
-
NIS2

ISPS Code (IMO / SOLAS XI-2)
For international ports and other security-critical environments, there are requirements for controlled access, security awareness, and ensuring that individuals in the area are familiar with applicable safety procedures.
National transport and port-related requirements
In operations with high demands on access control and safety procedures, organizations must be able to demonstrate that personnel and external actors have received relevant information—and that it has been understood.
NIS2
For organizations operating within essential and critical infrastructure, increased requirements apply to risk management, traceability, security awareness, and governance.
Full traceability when it truly matters
When requirements are managed manually through emails, signatures, PDFs, and local folders, it becomes difficult to track who did what, when, and against which version of a document.
With Inphiz, organizations can instead demonstrate:
- who received information
- who approved what
- when it happened
- which version applied
- which requirements were fulfilled at a given point in time
This makes a difference both in daily operations and during audits, incident investigations, or inspections.
Especially valuable for external actors
One of the biggest challenges in many organizations is managing contractors, suppliers, and subcontractors in a secure and consistent way.
Inphiz enables external actors to follow the same structured process for:
- onboarding
- information distribution
- document confirmation
- competency requirements
- traceable status
This reduces manual work and strengthens control across the entire chain.
A complementary layer to physical security
Inphiz does not replace identity systems or IAM.
Inphiz strengthens them.
IAM ensures who the person is and what access can be assigned.
Inphiz ensures that the person has met the right requirements to actually receive or retain that access.
It is in the combination of identity, validation, and traceability that a modern and sustainable security model emerges.
A secure technical foundation for operational processes